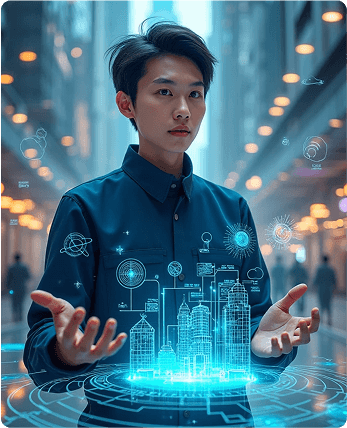
Unparalleled Cybersecurity: Our top-notch team of experts is dedicated to protecting your valuable data from any cyber threats. With cutting-edge technology and state-of-the-art software, we ensure that your digital world remains impenetrable. trustworthy and reliable: Our clients trust us because we deliver what



 Cyber Security
Cyber Security